-
Latest Version
Java JRE 8 Update 491 (64-bit) LATEST
-
Review by
-
Operating System
Windows 7 64 / Windows 8 64 / Windows 10 64 / Windows 11
-
User Rating
Click to vote -
Author / Product
-
Filename
jre-8u491-windows-x64.exe
-
MD5 Checksum
c127d266f40807796f06bbbc114ae24b
It's also integral to the intranet applications and other e-business solutions that are the foundation of corporate computing.
It provides the libraries, the Java Virtual Machine, and other components to run applets and applications written in the Java programming language.
In addition, two key deployment technologies are part of the JRE: Java Plug-in, which Enables Applets to Run in Popular Browsers; and Web Start, which deploys standalone applications over a network. Many cross-platform applications also require Java to operate properly.
It is a programming language and computing platform first released by Sun Microsystems in 1995. There are lots of applications and websites that will not work unless you have Java installed, and more are created every day.
The program is fast, secure, and reliable. From laptops to data centers, game consoles to scientific supercomputers, and cell phones to the Internet, Java is everywhere! It is at the heart of the digital lifestyle. It's the platform for launching careers, exploring human-to-digital interfaces, architecting the world's best applications, and unlocking innovation everywhere—from garages to global organizations.
Main Features
- Java Virtual Machine (JVM): JRE includes a Java Virtual Machine (JVM), which is responsible for executing Java bytecode.
- Class Libraries: It includes a set of class libraries that provide a wide range of functionality for Java programs. These libraries include collections, I/O, networking, security, and many other features.
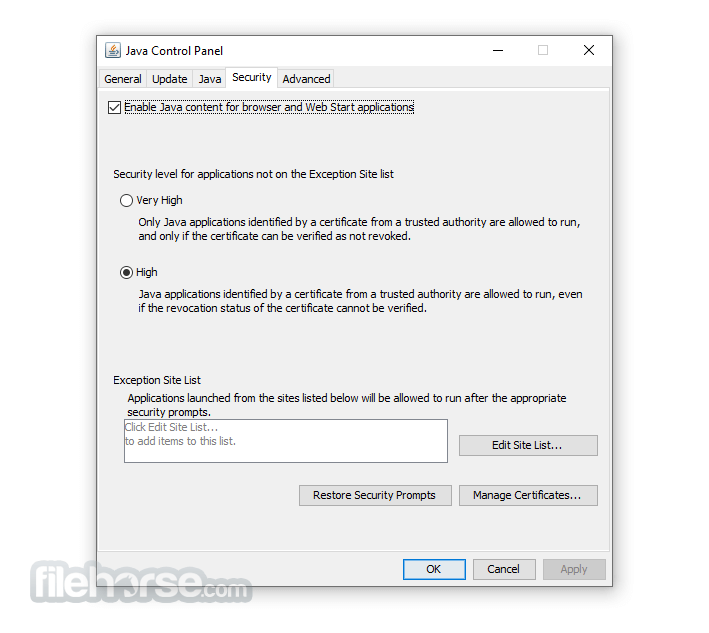
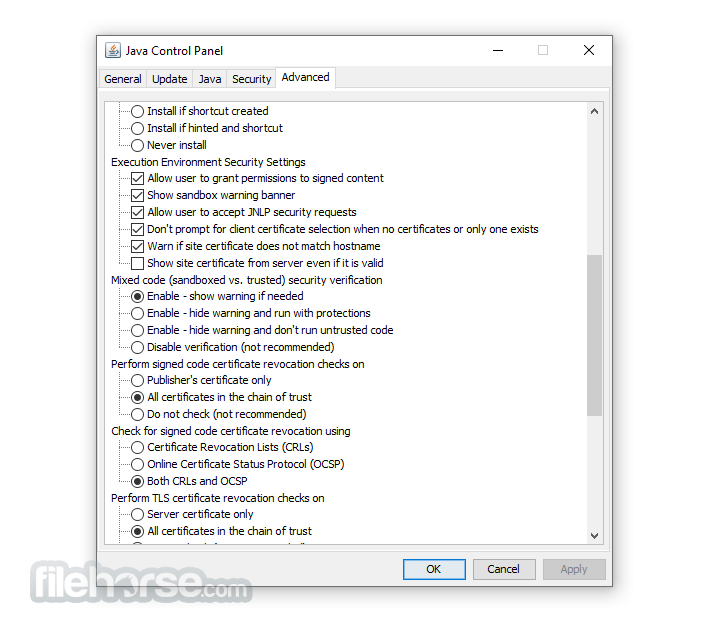
- Security: It provides a robust security model that ensures that Java programs run in a secure environment. It includes features such as sandboxing, code signing, and permission-based access control.
- Automatic Memory Management: It includes automatic memory management, which means that the JVM automatically manages the allocation and deallocation of memory for Java programs.
- Platform Independence: Java programs that run on JRE are platform-independent, which means that they can run on any platform that has JRE installed, regardless of the underlying hardware or operating system.
- Internationalization: It provides support for internationalization and localization, which allows Java programs to run in different languages and regions.
- Deployment: It provides an easy and convenient way to deploy Java programs on various platforms, such as desktops, servers, and mobile devices.
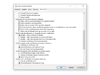
- Install JRE: First, you need to download and install the latest version of JRE from the official Java website or FileHorse.
- Write Java code: Next, write Java code using any text editor or integrated development environment (IDE) like Eclipse, NetBeans, or IntelliJ IDEA.
- Compile Java code: Once you have written your Java code, you need to compile it into byte code using the Java compiler. You can do this by running the "javac" command in the command prompt or terminal.
- Run Java program: After compiling your Java code, you can run it using the "java" command in the command prompt or terminal. This will execute the Java Virtual Machine (JVM) and load your byte code.
- Test and debug: You can test and debug your Java program using various tools provided by the IDE or through the command prompt. This will help you find and fix any errors or bugs in your code.
- Distribute Java program: Finally, once you have tested and debugged your Java program, you can distribute it to others. You can package your code into a JAR (Java Archive) file and distribute it to others who have JRE installed on their computers.
What is Java Runtime Environment (JRE)?
A: Java Runtime Environment (JRE) is a software package that provides the necessary components to run Java programs. It includes the Java Virtual Machine (JVM), libraries, and other components required to run Java applications.
What is the difference between JRE and JDK?
A: JDK (Java Development Kit) is a software development kit that includes the JRE, along with other tools like compilers and debuggers that are needed to develop Java applications. JRE is used to run Java programs, while JDK is used to develop them.
Can I run Java applications without installing JRE?
A: No, you need to install JRE in order to run Java applications.
How do I install JRE on my computer?
A: You can download and install the latest version of JRE from the official Java website. Follow the installation instructions provided on the website.
How do I check if JRE is installed on my computer?
A: You can check if JRE is installed on your computer by typing "java -version" in the command prompt or terminal. If JRE is installed, it will display the version information.
Is JRE free to use?
A: Yes, JRE is free to use for personal and commercial purposes.
Can I install multiple versions of JRE on my PC?
A: Yes, you can install multiple versions of JRE on your computer. However, it is recommended to use the latest version of JRE to ensure security and performance.
Can I uninstall older versions of JRE after installing a new version?
A: Yes, you can uninstall older versions of JRE after installing a new version. It is recommended to keep only the latest version of JRE installed on your computer.
Do I need to update JRE regularly?
A: Yes, it is recommended to update JRE regularly to ensure security and performance. Java updates usually contain bug fixes, security patches, and performance improvements.
Why should I upgrade to the latest version?
A: The latest version contains important enhancements to improve the performance, stability, and security of the applications that run on your machine. Installing this free update will ensure that your applications continue to run safely and efficiently.
What will I get when I download software?
A: The Java Runtime Environment 64-bit (JRE desktop app) is what you get when you download software. The JRE consists of the Java Virtual Machine (JVM), Java platform core classes, and supporting Java platform libraries. The JRE is the runtime portion of the software, which is all you need to run it in your Web browser.
What is Java Plug-in software?
A: The program is a component of the (JRE). The JRE allows applets written in the programming language to run inside various internet browsers. The Plug-in software is not a standalone program and cannot be installed separately.
I have heard the terms Virtual Machine and JVM. Is this software?
A: The Virtual Machine is only one aspect of software that is involved in web interaction. The Java Virtual Machine is built right into your software download and helps run Java apps.
System Requirements
- OS: Windows 7, 8, 8.1, 10, 11, Windows Server 2012, Windows Server 2016, and Windows Server 2019
- Processor: It requires a minimum of a Pentium 2 266 MHz processor, although a faster processor is recommended for optimal performance.
- Memory: It requires a minimum of 128 MB of RAM, although a larger amount of RAM is recommended for running complex Java programs.
- Disk space: It requires a minimum of 124 MB of disk space for installation, although a larger amount of disk space is recommended for running Java programs.
- Display: It requires a minimum display resolution of 800 x 600 pixels, although a higher resolution is recommended for better display quality.
- Widely Supported Language
- Platform Independence
- Robust Standard Library
- Automatic Memory Management
- Strong Community Support
- Slower Execution Speed
- Steeper Learning Curve
- Verbosity of Code
Overall, Java Runtime Environment (JRE) is a software environment that provides a runtime platform for running Java programs. It includes a Java Virtual Machine (JVM), class libraries, and other features that make it easy for developers to create and run Java applications.
JRE is a powerful and flexible platform that offers features such as platform independence, automatic memory management, security, and internationalization. This makes it an ideal choice for developing and running applications on various platforms, including desktops, servers, and mobile devices.
All in all, Java Runtime Environment (JRE) provides a reliable and robust platform for running Java applications, making it an essential tool for Java developers and users.
Note: When your installation completes, you may need to restart your browser (close all browser windows and re-open) to enable the installation.
Also Available: Java Runtime Environment (32-bit) and Java Runtime Environment for Mac
What's new in this version:
JDK 8u491 contains IANA time zone data 2026a which contains the following changes since the previous update:
- Several code changes for compatibility with FreeBSD
- The only changed data are leap second table expiration and pre-1976 time in Baja California
- Moldova has used EU transition times since 2022
- The "right" TZif files are no longer installed by default
- -DTZ_RUNTIME_LEAPS=0 disables runtime support for leap seconds
- TZif files are no longer limited to 50 bytes of abbreviations
- zic is no longer limited to 50 leap seconds
- Several integer overflow bugs have been fixed
New Features:
security-libs/java.security ➜ Enhanced keytool Password Handling When Output Is Redirected (JDK-8354469):
- The keytool command reads passwords from the system console to prevent them from being displayed on the screen. However, the console is usually available only when both the standard input and output streams are not redirected. Previously, if the standard output stream was redirected into a file or another command, the console was unavailable and the input password was echoed on the screen. This enhancement improves password handling to ensure that the password is not displayed on the screen even if the standard output stream is redirected. This enhancement has also been made to the jarsigner command and the JAAS TextCallbackHandler API.
security-libs/java.security ➜ Oracle JDK src.zip File Now Includes Source Code for the JSSE/JCE/JGSS Components (JDK-8369608):
- The <java-home>/lib/src.zip file distributed with the Oracle JDK now contains sources for JCE, JGSS, and JSSE. Debugging tools can now examine or display most of the security source files.
security-libs/java.security➜ New Security Property jdk.crypto.disabledAlgorithms for Restricting Algorithms at the JCE layer (JDK-8244336):
- A new security property named jdk.crypto.disabledAlgorithms has been introduced to disable algorithms for JCE/JCA cryptographic services. Initially, this property only supports the Cipher, KeyStore, MessageDigest, and Signature services. This property is defined in the java.security file and initially no algorithms are disabled by default. However, this may change in the future. This security property can be overridden by a system property of the same name if applications need to re-enable algorithms.
Other Notes:
javafx/other ➜ Oracle JDK 8 Includes JavaFX for a Limited Time (JDK-8371301 (not public)):
- JavaFX is again included with JDK 8, although it has a shorter support timeline than JDK 8. Update releases of JDK 8 after March 2028 will not include JavaFX. Visit www.oracle.com/javase/javafx for details.
core-libs/java.net➜ Implementation of java.net.CookieStore.getURIs() and get(URI) Methods Now Return an Immutable List (JDK-8365086):
- The JDK's implementation of the java.net.CookieStore interface has been updated to return an immutable java.util.List from the getURIs() and get(URI) methods. The updated implementation now matches the specification of these two methods.
security-libs/java.security➜ Distrust TLS Server Certificates Anchored by Chunghwa Root Certificates and Issued After March 17, 2026 (JDK-8369282):
- The JDK will stop trusting TLS server certificates issued after March 17, 2026 and anchored by Chunghwa root certificates, in line with similar plans announced by Google and Mozilla.
- TLS server certificates issued on or before March 17, 2026 will continue to be trusted until they expire. Certificates issued after that date, and anchored by the Certificate Authority listed in the table below, will be rejected.
- The restrictions are enforced in the JDK implementation (the SunJSSE Provider) of the Java Secure Socket Extension (JSSE) API. A TLS session will not be negotiated if the server's certificate chain is anchored by any of the Certificate Authorities in the table below and the certificate has been issued after March 17, 2026.
An application will receive an exception with a message indicating the trust anchor is not trusted, for example:
- "TLS Server certificate issued after 2026-03-17 and anchored by a distrusted legacy Chunghwa root CA: OU=ePKI Root Certification Authority, O="Chunghwa Telecom Co., Ltd." C=TW"
- The JDK can be configured to trust these certificates again by removing "CHUNGHWA_TLS" from the jdk.security.caDistrustPolicies security property in the java.security configuration file.
Fixed:
- JDK-8162545 client-libs/2d Mac build failure
- JDK-8223045 client-libs/2d GraphicsEnvironment does not detect resolution changes in multiscreen systems
- JDK-8373727 client-libs/2d New XBM images parser regression: only the first line of the bitmap array is parsed
- JDK-6899304 client-libs/java.awt java.awt.Toolkit.getScreenInsets(GraphicsConfiguration) returns incorrect values
- JDK-8372756 client-libs/java.awt Mouse additional buttons and horizontal scrolling are broken on XWayland GNOME >= 47 after JDK-8351907
- JDK-8372534 client-libs/java.awt Update Libpng to 1.6.51
- JDK-8372048 client-libs/java.awt Performance improvement on Linux remote desktop
- JDK-8375063 client-libs/java.awt Update Libpng to 1.6.54
- JDK-8372977 client-libs/java.awt Unnecessary gthread-2.0 loading
- JDK-8366261 core-libs/java.io Provide utility methods for sun.security.util.Password
- JDK-8048192 core-libs/java.nio (bf) Out of direct buffer memory message should include the limits
- JDK-8228343 core-svc/tools JCMD and attach fail to work across Linux Container boundary
- JDK-8371052 javafx/media Update libFFI to 3.5.2
- JDK-8377099 javafx/web Additional WebKit 623.1 fixes from WebKitGTK 2.50.4
- JDK-8377930 javafx/web Additional WebKit 623.1 fixes from WebKitGTK 2.50.5
- JDK-8368572 javafx/web Update WebKit to 623.1
- JDK-8380557 javafx/web Additional WebKit 623.1 fixes from WebKitGTK 2.50.6
- JDK-8375549 security-libs/java.security ConcurrentModificationException if jdk.crypto.disabledAlgorithms has multiple entries with known oid
- JDK-8374555 security-libs/java.security No need for visible input warning in s.s.u.Password when not reading from System.in
- JDK-8186831 security-libs/org.ietf.jgss:krb5 Kerberos ignores PA-DATA with a non-null s2kparams
- JDK-8336695 xml/jaxp Update Commons BCEL to Version 6.10.0
 OperaOpera 132.0 Build 5905.22 (64-bit)
OperaOpera 132.0 Build 5905.22 (64-bit) AdsPowerAdsPower - Antidetect Browser
AdsPowerAdsPower - Antidetect Browser PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit)
PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit) BlueStacks AIBlueStacks AI
BlueStacks AIBlueStacks AI OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum CapCutCapCut Desktop 8.7.0
CapCutCapCut Desktop 8.7.0 PC RepairPC Repair Tool 2026
PC RepairPC Repair Tool 2026 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 100 Million Traders
TradingViewTradingView - Trusted by 100 Million Traders Forza HorizonForza Horizon 6
Forza HorizonForza Horizon 6

Comments and User Reviews