-
Latest Version
.NET Framework 4.8.1 LATEST
-
Review by
-
Operating System
Windows 8 / Windows 10 / Windows 11
-
User Rating
Click to vote -
Author / Product
-
Filename
ndp481-devpack-enu.exe
-
MD5 Checksum
c1fb4bd5b4a2af2cd7a993c998ee26e3
With a rich class library and support for multiple programming languages, .NET Framework 4.8 empowers developers to create robust and efficient applications for various platforms.
Main Features
Enhanced Performance: It comes with performance improvements that optimize the execution of applications, resulting in faster and more responsive user experiences.
Security Improvements: Security is a top priority in this release, with features like improved cryptography, enhanced security protocols, and mitigations against potential vulnerabilities.
WPF and Windows Forms Updates: The framework includes updates to Windows Presentation Foundation (WPF) and Windows Forms, offering better compatibility, stability, and additional features for creating rich and interactive user interfaces.
Asynchronous Programming: Asynchronous programming is made easier with the async and await keywords, enabling developers to create more responsive applications without blocking the main thread.
Garbage Collection Enhancements: The Garbage Collector has been improved, leading to better memory management and overall application stability.
High DPI Support: With the proliferation of high-resolution displays, it provides enhanced support for high DPI scenarios, ensuring that applications look crisp and clear on any screen.
User Interface
The user interface of .NET Framework is not a standalone interface, as it primarily serves as a foundation for developers to create their own user interfaces using technologies like WPF and Windows Forms.
However, the framework's improvements in these areas indirectly contribute to creating more polished and visually appealing user interfaces.
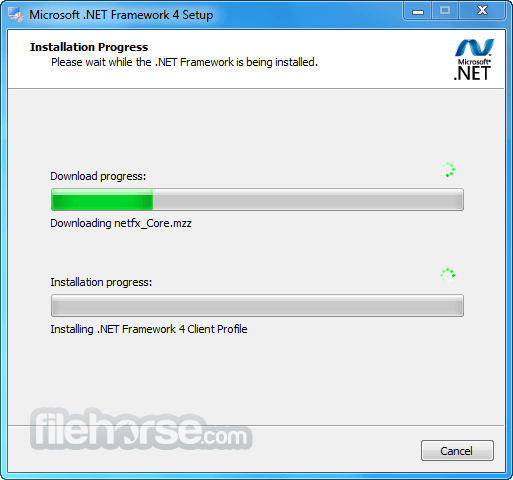
Installation and Setup
Installing the .NET Framework 4.8 is a straightforward process. It is often included with Windows updates, and you can also download the installer from the Microsoft website or FileHorse.
The installation wizard guides you through the process, and once installed, the framework is ready to be used for application development.
How to Use
Using the app involves integrating it into your development environment and leveraging its class library to build applications. Developers can choose from various programming languages, such as C#, VB.NET, and F#, to write code that targets the framework.
Microsoft provides extensive documentation, tutorials, and samples to help developers get started.
FAQs
What is the purpose of the .NET Framework?
The .NET Framework is a software framework that provides a runtime environment and a comprehensive class library for developing and running applications on Windows-based platforms.
Is .NET Framework only for Windows desktop applications?
While the .NET Framework was initially designed for Windows desktop applications, it has evolved to support a wider range of application types, including web applications, cloud services, and mobile apps.
How does .NET Framework differ from .NET Core and .NET 5+?
The app is a mature framework primarily used for Windows applications. .NET Core and .NET 5+ (now known as .NET 6+) are successors that offer cross-platform support and a more modular architecture.
Is .NET Framework 4.8 the latest version?
No, .NET Framework 4.8 is one of the final versions in the .NET Framework line. Microsoft's focus has shifted to .NET Core and, subsequently, to .NET 5+ (.NET 6+).
Can I migrate my existing .NET Framework applications to newer platforms?
Yes, Microsoft provides tools and resources to help migrate applications from .NET Framework to .NET Core or .NET 5+. However, it may require some code adjustments due to architectural differences.
Alternatives
Java - A versatile programming language and platform that supports a wide range of applications, including desktop, web, and mobile.
Python - Known for its simplicity and readability, Python is widely used for web development, data analysis, and automation.
Node.js - Built on the JavaScript runtime, Node.js is popular for building scalable and high-performance network applications.
Pricing
The .NET Framework itself is free to use and is often included with Windows installations.
However, keep in mind that the cost of using the framework may be associated with the development tools, IDEs, and other technologies you use in conjunction with it.
System Requirements
It has system requirements that are tied to the Windows operating system version you're using.
It's important to refer to Microsoft's documentation for the specific requirements relevant to your environment.
PROS
- Mature and stable framework with a rich history.
- Comprehensive class library for various application types.
- Enhanced performance and security features.
- Strong integration with Windows-based platforms.
- Limited cross-platform support compared to modern alternatives.
- Not suitable for all application types, especially those targeting non-Windows platforms.
- Gradual shift of Microsoft's focus to newer platforms, making .NET Framework less relevant for new projects.
It has a legacy of powering countless Windows applications and services. While it remains a robust choice for Windows-focused development, it's important to recognize Microsoft's transition to more modern platforms like .NET Core and .NET 5+ for cross-platform and future-proof application development.
If your project requires Windows-specific features and compatibility, .NET Framework 4.8 is a dependable option. However, for new projects with cross-platform aspirations, exploring alternatives like .NET Core and other languages/frameworks might be more beneficial in the long run.
What's new in this version:
NET Framework 4.8.1 introduces new features in the following areas:
- Native support for Arm64
- WCAG2.1 compliant accessible tooltips
- Windows Forms – Accessibility Improvements
- Improved accessibility, which allows an application to provide an appropriate experience for users of Assistive Technology, is a major focus of .NET Framework 4.8.1. For information on accessibility improvements in .NET Framework 4.8.1, see What's new in accessibility in .NET Framework.
- .NET Framework 4.8.1 adds native Arm64 support to the .NET Framework family. So, your investments in the vast ecosystem of .NET Framework apps and libraries can now leverage the benefits of running workloads natively on Arm64—namely better performance when compared to running x64 code emulated on Arm64.
- Microsoft has a commitment to providing products and platforms that are accessible to everyone. .NET Framework 4.8.1 offers two Windows UI development platforms, both of which provide developers with the support necessary to create accessible applications. Over the past several releases, both Windows Forms and WPF have added new features and fixed numerous reliability issues related to accessibility. You can read more about the details of what was fixed or added in each release by visiting What’s new in accessibility in .NET Framework.
In this release, both Windows Forms and WPF have made improvements to the handling of tooltips to make them more accessible. In both cases, tooltips now comply with the guidelines set forth in the WCAG2.1 content on Hover or Focus guidance. The requirements for tooltips are:
- Tooltips must display either via mouse hover or by keyboard navigation to the control
- Tooltips should be dismissable. That is, a simple keyboard command like Esc should dismiss the tooltip.
- Tooltips should be hoverable. Users should be able to place their mouse cursor over the tooltip. This enables scenarios like using magnifier to be able to read the tooltip for low-vision users.
- Tooltips should be persistent. Tooltips should not automatically disappear after a certain amount of time has elapsed. Rather, tooltips should be dismissed by the user moving their mouse to another control or by a keyboard command.
- In Windows Forms, this support is only available on Windows 11 or later operating systems. Windows Forms is a thin managed wrapper around the Windows API, and the new tooltip behavior only became available in Windows 11. WPF has no operating system version dependencies for its accessible tooltips.
- WPF had implemented most of the requirements for WCAG2.1 compliant tooltips in .NET Framework 4.8. In this release, WPF improved the experience by ensuring that a tooltip in the current window can easily be dismissed by using the Esc key, the Ctrl key (by itself), or by the combination Ctrl+Shift+F10. The scope of the escape key was reduced in this release to apply only to the current window. Previously it applied to any open tooltip in the application.
- Windows Forms was the first Windows UI stack created for .NET Framework. As such, it was originally created to utilize legacy accessibility technology, which doesn't meet current accessibility requirements. In this release, Windows Forms has addressed a number of issues. For a complete list of the accessibility related changes, visit What’s new in accessibility in .NET Framework.
The highlights of Windows Forms improvements in .NET Framework 4.8.1 are:
- Text pattern support– Windows Forms added support for the UIA Text Pattern. This pattern enables assistive technology to traverse the content of a TextBox or similar text-based control letter by letter. It enables text to be selected within the control and changed, and new text to be inserted at the cursor. Windows Forms added this support for TextBox, DataGridView cells, ComboBox controls, and more.
- Address contrast issues– In several controls, Windows Forms has changed the contrast ratio of selection rectangles to be darker and more visible
Fixed several DataGridView issues:
- The scrollbar names have been updated to be consistent
- Narrator is now able to focus on empty DataGridView cells
- Developers are able to set the localized control type property for Custom DataGridView cells
- The link color for DataGridViewLink cells has been updated to have better contrast with the background
 OperaOpera 132.0 Build 5905.22 (64-bit)
OperaOpera 132.0 Build 5905.22 (64-bit) AdsPowerAdsPower - Antidetect Browser
AdsPowerAdsPower - Antidetect Browser PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit)
PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit) BlueStacks AIBlueStacks AI
BlueStacks AIBlueStacks AI OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum CapCutCapCut Desktop 8.7.0
CapCutCapCut Desktop 8.7.0 PC RepairPC Repair Tool 2026
PC RepairPC Repair Tool 2026 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 100 Million Traders
TradingViewTradingView - Trusted by 100 Million Traders Forza HorizonForza Horizon 6
Forza HorizonForza Horizon 6


Comments and User Reviews