-
Latest Version
-
Operating System
Windows XP64 / Vista64 / Windows 7 64 / Windows 8 64 / Windows 10 64
-
User Rating
Click to vote -
Author / Product
-
Filename
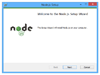
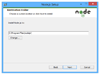
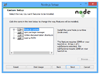
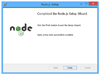
node-v12.8.1-x64.msi
-
MD5 Checksum
39a7f8d0b6988cdc111ef4b0ea83d255
Sometimes latest versions of the software can cause issues when installed on older devices or devices running an older version of the operating system.
Software makers usually fix these issues but it can take them some time. What you can do in the meantime is to download and install an older version of Node.js 12.8.1 (64-bit).
For those interested in downloading the most recent release of Node.js (64-bit) or reading our review, simply click here.
All old versions distributed on our website are completely virus-free and available for download at no cost.
We would love to hear from you
If you have any questions or ideas that you want to share with us - head over to our Contact page and let us know. We value your feedback!
What's new in this version:
Fixed:
- “Data Dribble”: The attacker requests a large amount of data from a specified resource over multiple streams. They manipulate window size and stream priority to force the server to queue the data in 1-byte chunks. Depending on how efficiently this data is queued, this can consume excess CPU, memory, or both, potentially leading to a denial of service.
- “Ping Flood”: The attacker sends continual pings to an HTTP/2 peer, causing the peer to build an internal queue of responses. Depending on how efficiently this data is queued, this can consume excess CPU, memory, or both, potentially leading to a denial of service.
- “Resource Loop”: The attacker creates multiple request streams and continually shuffles the priority of the streams in a way that causes substantial churn to the priority tree. This can consume excess CPU, potentially leading to a denial of service.
- “Reset Flood”: The attacker opens a number of streams and sends an invalid request over each stream that should solicit a stream of RST_STREAM frames from the peer. Depending on how the peer queues the RST_STREAM frames, this can consume excess memory, CPU, or both, potentially leading to a denial of service.
- “Settings Flood”: The attacker sends a stream of SETTINGS frames to the peer. Since the RFC requires that the peer reply with one acknowledgement per SETTINGS frame, an empty SETTINGS frame is almost equivalent in behavior to a ping. Depending on how efficiently this data is queued, this can consume excess CPU, memory, or both, potentially leading to a denial of service.
- “0-Length Headers Leak”: The attacker sends a stream of headers with a 0-length header name and 0-length header value, optionally Huffman encoded into 1-byte or greater headers. Some implementations allocate memory for these headers and keep the allocation alive until the session dies. This can consume excess memory, potentially leading to a denial of service.
- “Internal Data Buffering”: The attacker opens the HTTP/2 window so the peer can send without constraint; however, they leave the TCP window closed so the peer cannot actually write (many of) the bytes on the wire. The attacker then sends a stream of requests for a large response object. Depending on how the servers queue the responses, this can consume excess memory, CPU, or both, potentially leading to a denial of service.
C- “Empty Frames Flood”: The attacker sends a stream of frames with an empty payload and without the end-of-stream flag. These frames can be DATA, HEADERS, CONTINUATION and/or PUSH_PROMISE. The peer spends time processing each frame disproportionate to attack bandwidth. This can consume excess CPU, potentially leading to a denial of service.
 OperaOpera 109.0 Build 5097.80 (64-bit)
OperaOpera 109.0 Build 5097.80 (64-bit) iTop VPNiTop VPN 5.5.0 - Fast, Safe & Secure
iTop VPNiTop VPN 5.5.0 - Fast, Safe & Secure PhotoshopAdobe Photoshop CC 2024 25.7 (64-bit)
PhotoshopAdobe Photoshop CC 2024 25.7 (64-bit) PC RepairPC Repair 1.0.3
PC RepairPC Repair 1.0.3 Opera GXOpera GX 109.0.5097.79 (64-bit)
Opera GXOpera GX 109.0.5097.79 (64-bit) Adobe AcrobatAdobe Acrobat Pro 2024.002.20759
Adobe AcrobatAdobe Acrobat Pro 2024.002.20759 BlueStacksBlueStacks - Play on PC 5.21.205
BlueStacksBlueStacks - Play on PC 5.21.205 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game SwifDoo PDFSwifDoo PDF 2.0.5.8
SwifDoo PDFSwifDoo PDF 2.0.5.8 TradingViewTradingView - Trusted by 60 Million Traders
TradingViewTradingView - Trusted by 60 Million Traders




Comments and User Reviews