-
Latest Version
Wireshark 4.6.6 (64-bit) LATEST
-
Review by
-
Operating System
Windows 8 (64-bit) / Windows 10 (64-bit) / Windows 11
-
User Rating
Click to vote -
Author / Product
-
Filename
Wireshark-4.6.6-x64.exe
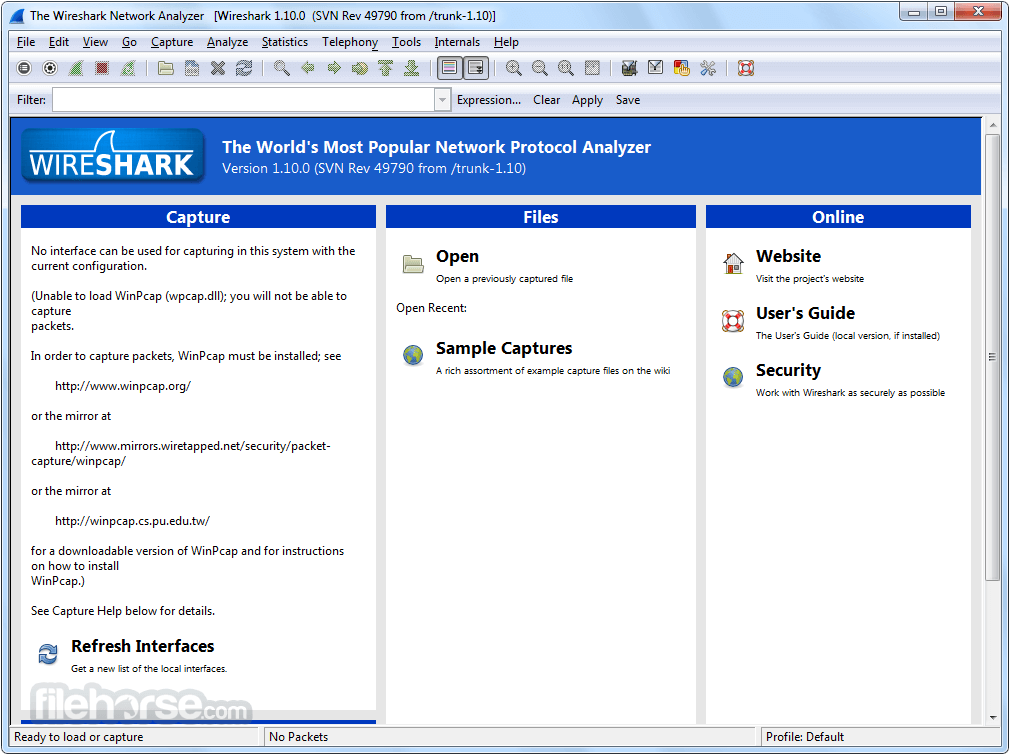
An open-source network protocol analyzer that lets you capture and interactively browse the traffic running on a computer network.
Originally named Ethereal, it was rebranded as Wireshark in 2006 and has since become a go-to tool for network troubleshooting, analysis, software and communication protocol development, and education. It's available for Windows, macOS, Linux, and other Unix-like operating systems.
The app was written by networking experts around the world and is an example of the power of open-source. Wireshark 64-bit is used by network professionals around the world for analysis, troubleshooting, software and protocol development, and education.
The program has all of the standard features you would expect in a protocol analyzer, and several features not seen in any other product. Its open source license allows talented experts in the networking community to add enhancements.
Highlights
- Deep inspection of hundreds of protocols, with more being added all the time
- Live capture and offline analysis
- Standard three-pane packet browser
- Multi-platform: Runs on Windows, Linux, macOS, Solaris, FreeBSD, NetBSD, and many others
- Captured network data can be browsed via a GUI, or via the TTY-mode TShark utility
- The most powerful display filters in the industry
- Rich VoIP analysis
- Read/write many different capture file formats: tcpdump (libpcap), Pcap NG, Catapult DCT2000, Cisco Secure IDS iplog, Microsoft Network Monitor, Network General Sniffer® (compressed and uncompressed), Sniffer® Pro, and NetXray®, Network Instruments Observer, NetScreen snoop, Novell LANalyzer, RADCOM WAN/LAN Analyzer, Shomiti/Finisar Surveyor, Tektronix K12xx, Visual Networks Visual UpTime, WildPackets EtherPeek/TokenPeek/AiroPeek, and many others
- Capture files compressed with gzip can be decompressed on the fly
- Live data can be read from Ethernet, IEEE 802.11, PPP/HDLC, ATM, Bluetooth, USB, Token Ring, Frame Relay, FDDI, and others (depending on your platform)
- Decryption support for many protocols, including IPsec, ISAKMP, Kerberos, SNMPv3, SSL/TLS, WEP, and WPA/WPA2
- Coloring rules can be applied to the packet list for quick, intuitive analysis
- Output can be exported to XML, PostScript®, CSV, or plain text
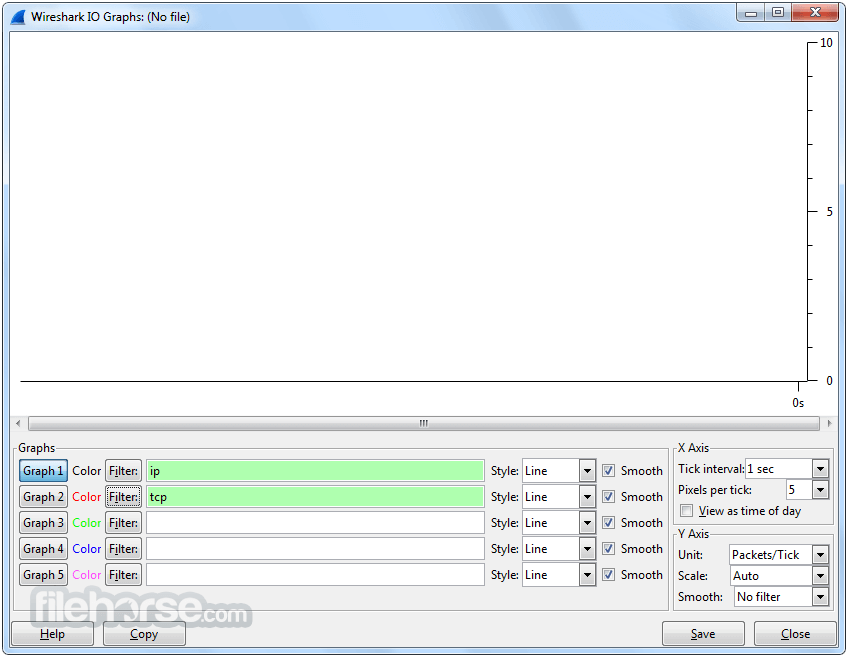
- Packet Analysis: It captures data packets from a network in real-time or from saved capture files for in-depth analysis.
- Deep Inspection: Users can inspect hundreds of protocols, including Ethernet, IP, TCP, HTTP, DNS, and more, to diagnose network issues or investigate security incidents.
- Filtering: Advanced filtering capabilities allow users to sift through large volumes of data to focus on specific packets or protocols.
- Protocol Decoding: The app decodes packet contents into human-readable formats, aiding in understanding network communication.
- VoIP Analysis: Support for VoIP protocols enables analysis of voice and video communications.
- Exporting: Captured data can be exported to various file formats for further analysis or sharing.
- Extensibility: It offers a rich ecosystem of plugins and scripts for extending functionality.
It features a comprehensive graphical user interface (GUI) with multiple panes for packet display, packet details, packet list, and more. It provides color-coded packet highlighting for easy identification of various protocols and types of traffic.
Installation and Setup
Installing this program is straightforward on most platforms. Users can download the installer from the official website or FileHorse and follow the on-screen instructions. On Windows, it also offers an option to install WinPcap or Npcap for packet capture.
How to Use
- Launch the tool and select the network interface for capturing packets.
- Start capturing packets by clicking the "Start" button.
- Analyze captured packets in real-time or from saved capture files.
- Apply filters to focus on specific packets or protocols.
- Use built-in tools for deep packet inspection, protocol decoding, and analysis.
- Export relevant data for further investigation or reporting.
Can Wireshark 64bit capture encrypted traffic?
It can capture encrypted traffic, but it cannot decrypt it unless the user has access to the encryption keys.
Does Wireshark support wireless network capture?
Yes, it supports capturing packets from wireless networks, but it requires compatible hardware and drivers.
Is Wireshark legal to use?
Yes, the software is legal to use for network analysis and troubleshooting. However, using it for unauthorized interception of network traffic may be illegal in some jurisdictions.
Can Wireshark be used for cybersecurity purposes?
Yes, the program is commonly used by cybersecurity professionals for analyzing network traffic, detecting anomalies, and investigating security incidents.
What are some common troubleshooting scenarios where Wireshark is useful?
It can help troubleshoot network connectivity issues, performance problems, security breaches, and application communication errors, among others.
Pricing
Thge tool is open-source and available for FREE under the GNU General Public License.
System Requirements
The program is available for Windows, macOS, Linux, and other Unix-like operating systems. System requirements vary depending on the platform and usage scenario but generally include a reasonable amount of RAM and disk space for packet capture and analysis.
PROS
- Comprehensive protocol support
- Extensive filtering and analysis capabilities
- Open-source and free
- Active community and ongoing development
- Cross-platform compatibility
- Steep learning curve for beginners
- Requires understanding of networking concepts
- Limited support for decrypting encrypted traffic
- Resource-intensive for capturing and analyzing large data volumes
What's new in this version:
Fixes:
The following vulnerabilities have been fixed:
- wnpa-sec-2026-51 ROHC protocol dissector crash
The following bugs have been fixed:
- Wireshark crashes when run under Visual Studio on Windows
- Welcome page slide preferences are now available in the preferences window
- vwr: Read of uninitialized memory in pntoh16
- vwr: Read of uninitialized memory in find_signature
- Upgrades on Windows do not retain existing optional features unless explicitly requested, resulting in accidental removal of features
- Wireshark.exe version 4.6.5 is twice as large as version 4.6.4
- MACsec dissector global-buffer-overflow
- Wireshark 4.6.5 does not run on Windows 10 version 1809 (including Server 2019 and some LTSC versions)
- Fuzz job issue: fuzz-2026-05-02-14184750352.pcap
- packet-bacapp: rename aurth-request to auth-request
- Fuzz job issue: randpkt-2026-05-10-14293434231.pcap
New and Updated Features:
- The Windows installers now ship with Npcap 1.88. They previously shipped with Npcap 1.87
Updated Protocol Support:
- BACapp, BPv7, DB/IB GDS DB, Kafka, MACsec, PFCP, RF4CE, ROHC, RTPS-VT, SAPHDB, and SIP
New and Updated Capture File Support:
- JSON and VeriWave
Plugin Development Changes:
- On UN*X systems (excluding macOS when running from an app bundle, as with the official installer) extcap binaries are now searched for under the libexec directory by default, e.g., /usr/libexec/wireshark/extcap instead of /usr/lib64/wireshark/extcap or similar. This is the customary place for helper binaries, which as opposed to libraries do not need multiarch support. The location can be overridden via the environment variable WIRESHARK_EXTCAP_DIR. The extcap binaries shipped with Wireshark are installed in the new location, but third party extcaps may need packaging changes. This change was effective in version 4.6.0, but was not explicitly noted in the release notes previously. Note that some distributions do not use a libexec directory, such as Alpine Linux, which does not have multilib support. On such systems extcap binaries should be in the same location as before.
 OperaOpera 132.0 Build 5905.11 (64-bit)
OperaOpera 132.0 Build 5905.11 (64-bit) AdsPowerAdsPower - Antidetect Browser
AdsPowerAdsPower - Antidetect Browser PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit)
PhotoshopAdobe Photoshop CC 2026 27.7 (64-bit) BlueStacks AIBlueStacks AI
BlueStacks AIBlueStacks AI OKXOKX - Buy Bitcoin or Ethereum
OKXOKX - Buy Bitcoin or Ethereum CapCutCapCut Desktop 8.5.0
CapCutCapCut Desktop 8.5.0 PC RepairPC Repair Tool 2026
PC RepairPC Repair Tool 2026 Hero WarsHero Wars - Online Action Game
Hero WarsHero Wars - Online Action Game TradingViewTradingView - Trusted by 100 Million Traders
TradingViewTradingView - Trusted by 100 Million Traders Forza HorizonForza Horizon 6
Forza HorizonForza Horizon 6








Comments and User Reviews